Computer Repairs Brisbane: Keeping Your Devices Running Smoothly
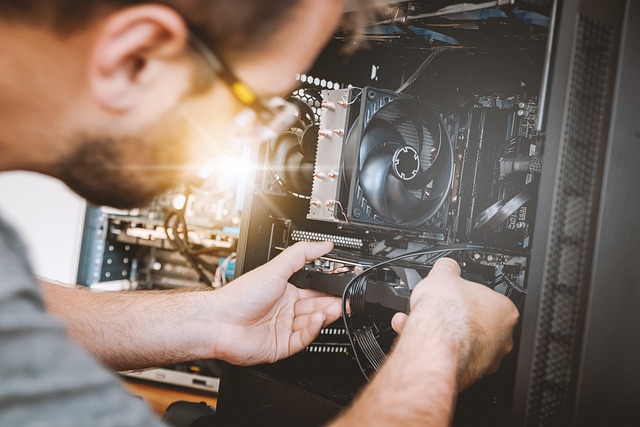
When it comes to computer repairs in Brisbane, it’s important to find reliable technicians who can fix your devices quickly
When it comes to computer repairs in Brisbane, it’s important to find reliable technicians who can fix your devices quickly

Have you ever wondered how your computer is able to run all the applications and software that you use every
Brisbane is home to a number of computer geeks, and it can be difficult to know who to trust when

If you’re looking for the best computer and electronics deals in Penrith, you need to visit one of the local

If you want to get rid of all the errors that are embedded deep inside the roots of your computer’s

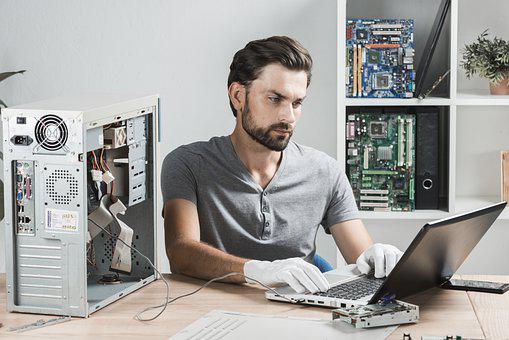
Laptops usually develop a wide range of problems from time to time. The batter can get damaged while the laptop

Expert computer repair services are just a call away. Call the computer technician Penrith to your home or office for

PCB panel design process requires some special consideration. First define the purpose of the panel. Plan early to increase the

Modern laptops are made to be slimmer, sleeker and much more powerful than earlier models. The batteries in these laptops

Most businesses in Sydney have realized how beneficial cloud hosting services are to their everyday operations. Cloud computing gives businesses the ability